Active Directory Configuration
Overview
Integration of SoftNAS® into Active Directory enables domain users to more securely share files and data in a corporate environment. Authentication is managed by Active Directory (AD) via Kerberos.
Kerberos tickets are issued to users authenticated to AD. When a user accesses a CIFS share managed by SoftNAS®, the ticket is then verified with AD to ensure it is authentic and valid before allowing access to the shares. Windows user IDs and groups (e.g.,Domain Users) are transparently and dynamically mapped from AD into SoftNAS® and Linux, making access seamless for Windows users.
When integrated into a domain environment, SoftNAS® becomes another member server of the domain - like any other Windows server joined to the domain.
Authorization and granular access controls are available to manage the level of access available to various users and user groups.
The following sections detail how to configure SoftNAS® for integration with AD and how to troubleshoot and resolve common issues that can arise during AD integration.
On Linux, Samba is used to provide access to CIFS for access from Windows-based systems. Samba uses a program called winbind, which binds Windows authentication and identities (e.g., AD users and groups) with Linux, and automatically maps Windows users and groups to Linux users and groups.
Please use the following process to integrate AD with SoftNAS® and Linux with Samba.
Prerequisites:
- A DNS Server must be configured
- An existing Active Directory set-up and running
- Prior to configuring the Active Directory Wizard, you must add the server IP address as Domain name server within the Hosts and DNS Clients applet, found in Network Settings in the Storage Administration pane.
Active Directory Wizard
Configure AD using the Active Directory Wizard. This enables integration automation with AD.
After entering some basic networking details to enable SoftNAS® to communicate within the AD environment, SoftNAS® will automatically set up the integration with AD, and will even run a final verification stage to ensure that everything is working smoothly.
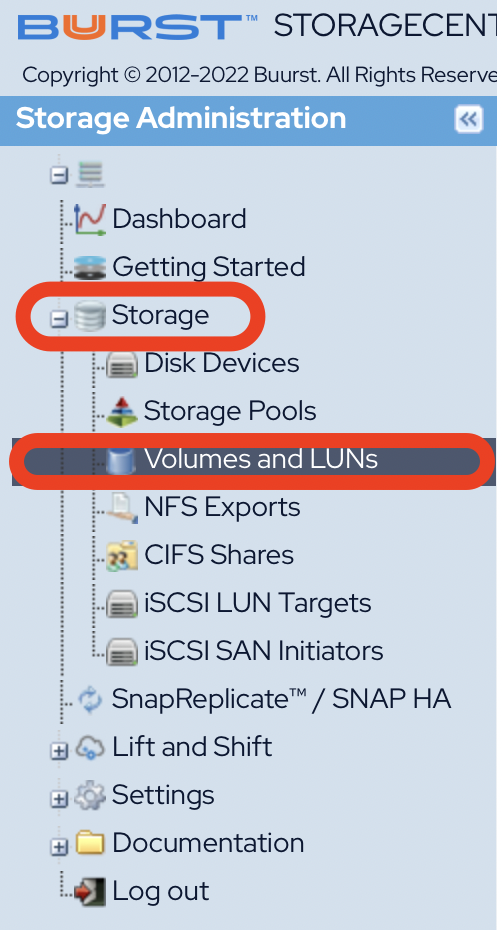
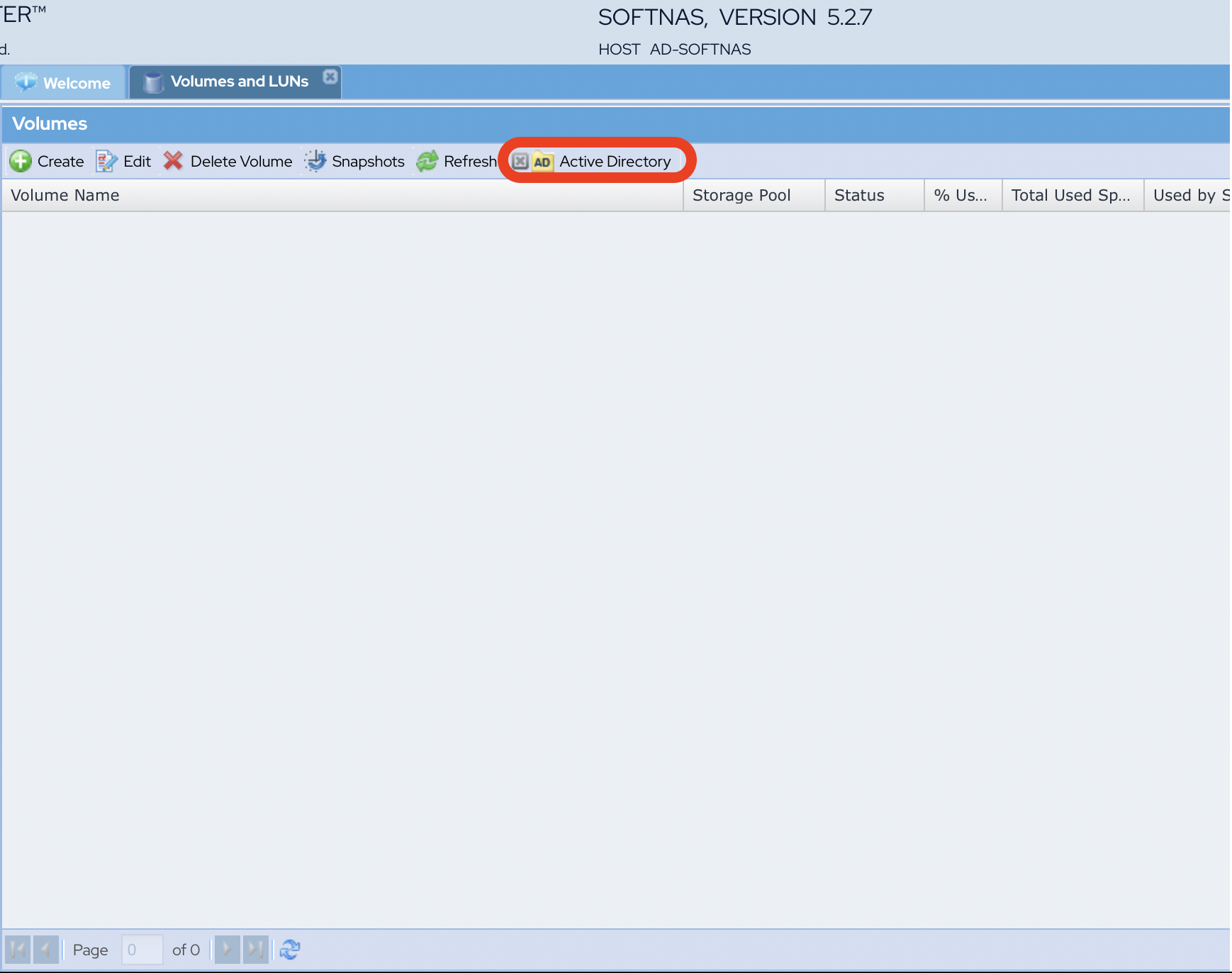
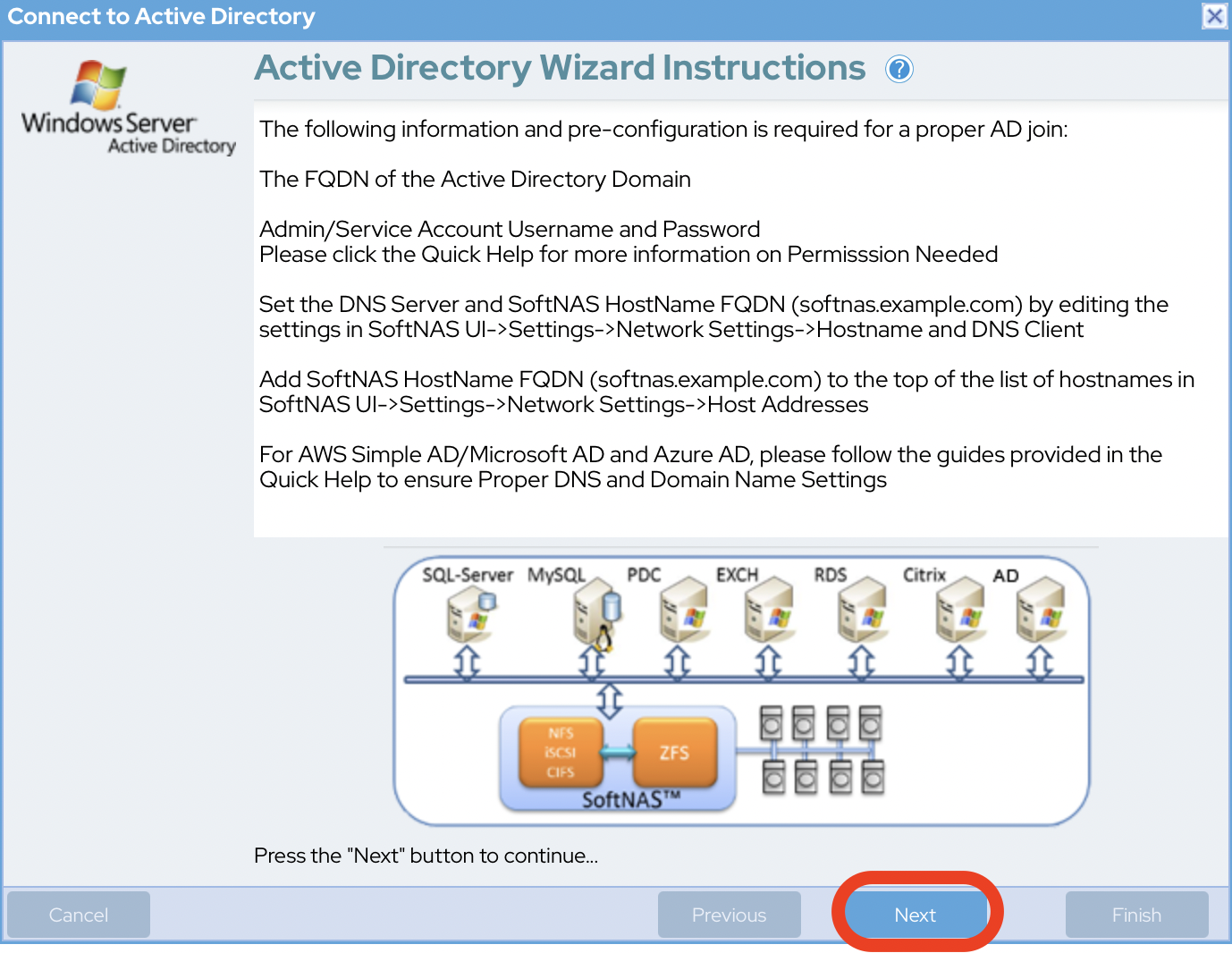
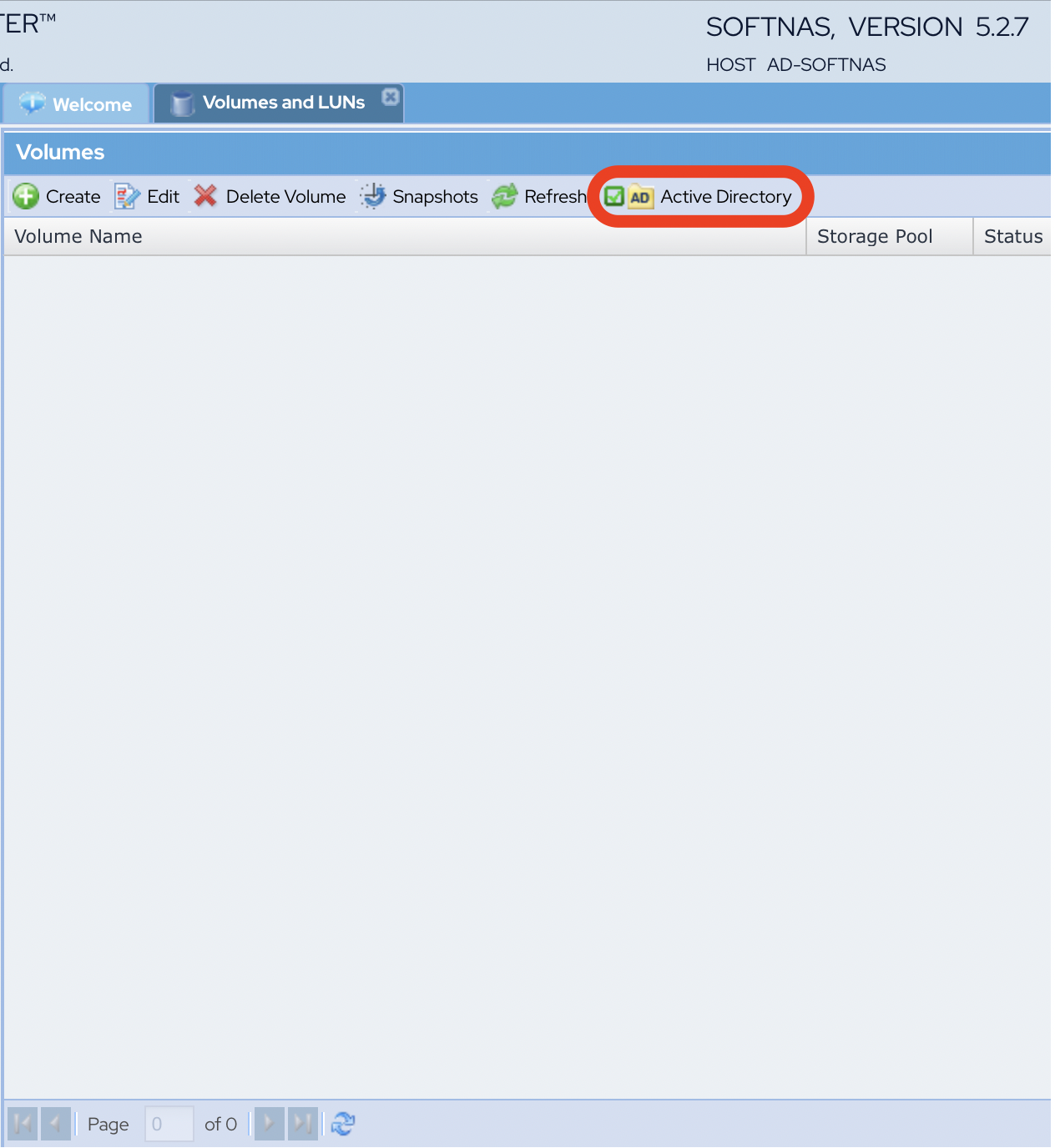
- Navigate to Storage > Volumes and LUNS and click on the Active Directory button. The AD Wizard instructions are displayed.
- Click Next to proceed.
- Provide the following information when prompted:
- Domain Name
- Netbios Domain Name
- User ID
- Password
- When done, click Next to proceed.
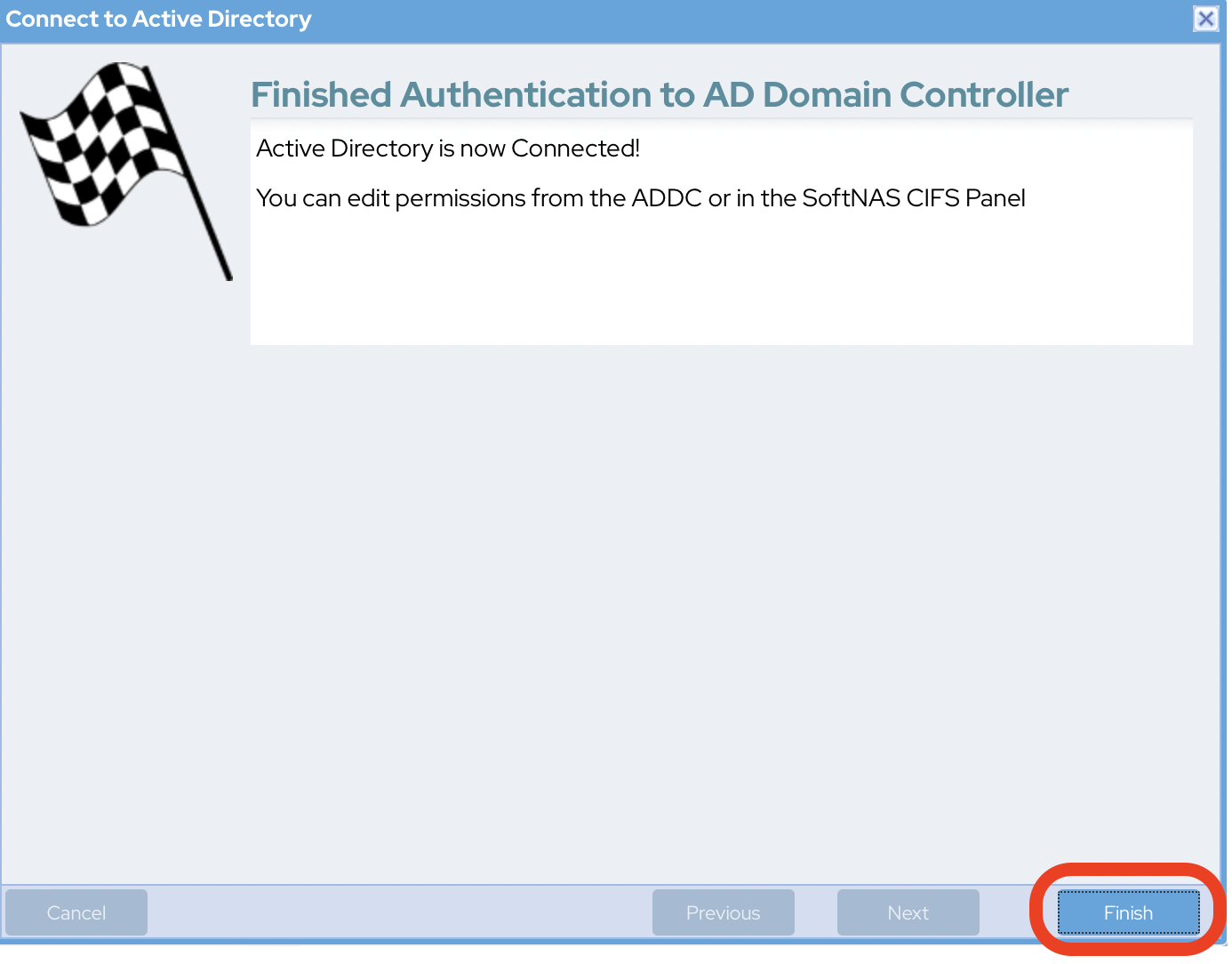
- Click Finish to complete the joining process.
- Successful joining of Active Directory is signified with a green checkmark next to Active
Congratulations, you are now ready to administer SoftNAS with your Azure AD DS administrative account!
Success Verification
You might need to click Refresh to see the green checkmark next to Active Directory.
Adding HA pairings to Active Directory
If connecting SoftNAS instances in a High Availability pairing to Active Directory, you MUST perform the process above twice, once on each node.
Active Directory configurations do not carry over to the second node automatically because the target node's NAS services (amongst others) are not running while the node is dormant.
Settings cannot be automatically triggered upon takeover. In order for the second instance to remain in Active Directory after a failover the second node must be added as well.