[SoftNAS KB]: How To Configure Existing AD (for 2008 and up) with NIS Server to SoftNAS Samba
Symptoms
Many Cloud environments use a hybrid of Windows and Linux servers for their hosted applications. Keeping proper ownership between Windows Active Directory/NIS and Linux NFS is vital for security and the operation of applications that depend on proper file user and group ownership.
SoftNAS uses Sernet Samba to accomplish CIFS and Active Directory integration. SoftNAS can also sync these permissions and File Ownerships to NFSv4 Clients running Linux based Operating systems.
Purpose
In the following guide, we will provide step-by-step guidance on how to properly configure an existing Windows 2008/2008R2/2012/2012R2/2016 Active Directory with NIS server to sync users/UID and groups/GID to the SoftNAS Samba CIFS shares. These permissions will also sync to NFSv4 Linux clients that are also joined into the Domain/NIS.
- 1) The SoftNAS will need to be already joined to the Active Directory by following the instructions provided by the wizard in the SoftNAS UI → Volumes and LUNs→ Active Directory Wizard.
https://www.softnas.com/docs/softnas/v3/html/active_directory_configuration.html
- 2) The user and group IDs must be within the range configured in the smb.conf for this domain. Our example /etc/samba/smb.conf has added the following two lines:
idmap config SOFTNAS0:backend = ad idmap config SOFTNAS0:range = 10000-70000
- 3) Users primary group, for example Domain Users, must have the gidNumber attribute set. Otherwise Winbind is not able to list domain users.
- 4) Users must have at least the uidNumber and the gidNumber attribute set. When using the RFC2307 winbind NSS info mode(SoftNAS Uses this by Default), user accounts must also have the loginShell, unixHomeDirectory and primaryGroupID set.
- 5) Install Server for NIS on the computer that is running the Active Directory Users and Computers MMC snap-in. https://technet.microsoft.com/en-us/library/cc731178.aspx?ppud=4#BKMK_command
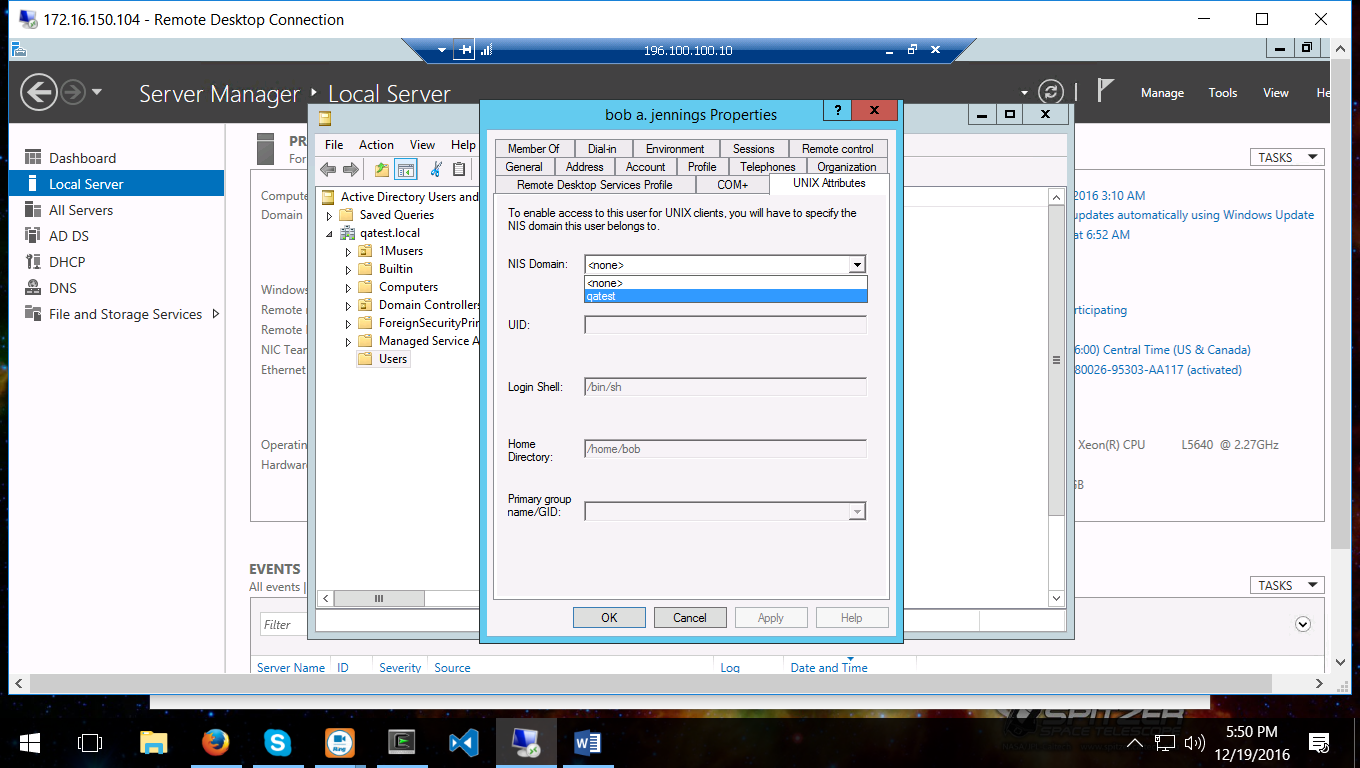
- 6) You can now access the Unix Attributes for Users and Groups
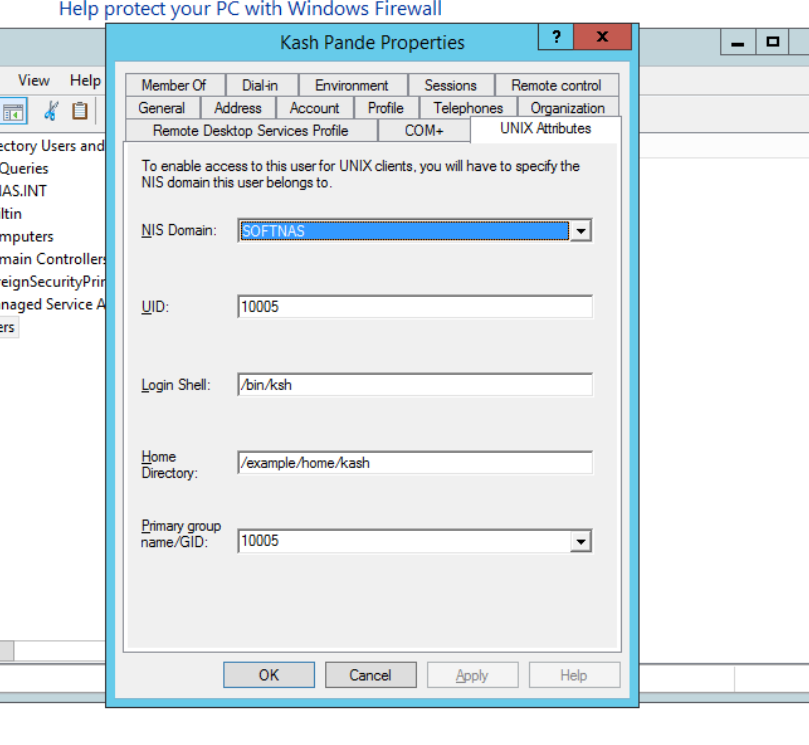
The example below shows the User Kash Pande with UID 10005, login shell, Home Directory, and Primary Group GID 10005.
This will need to be set for all users that will need to be synced to the SoftNAS Server.
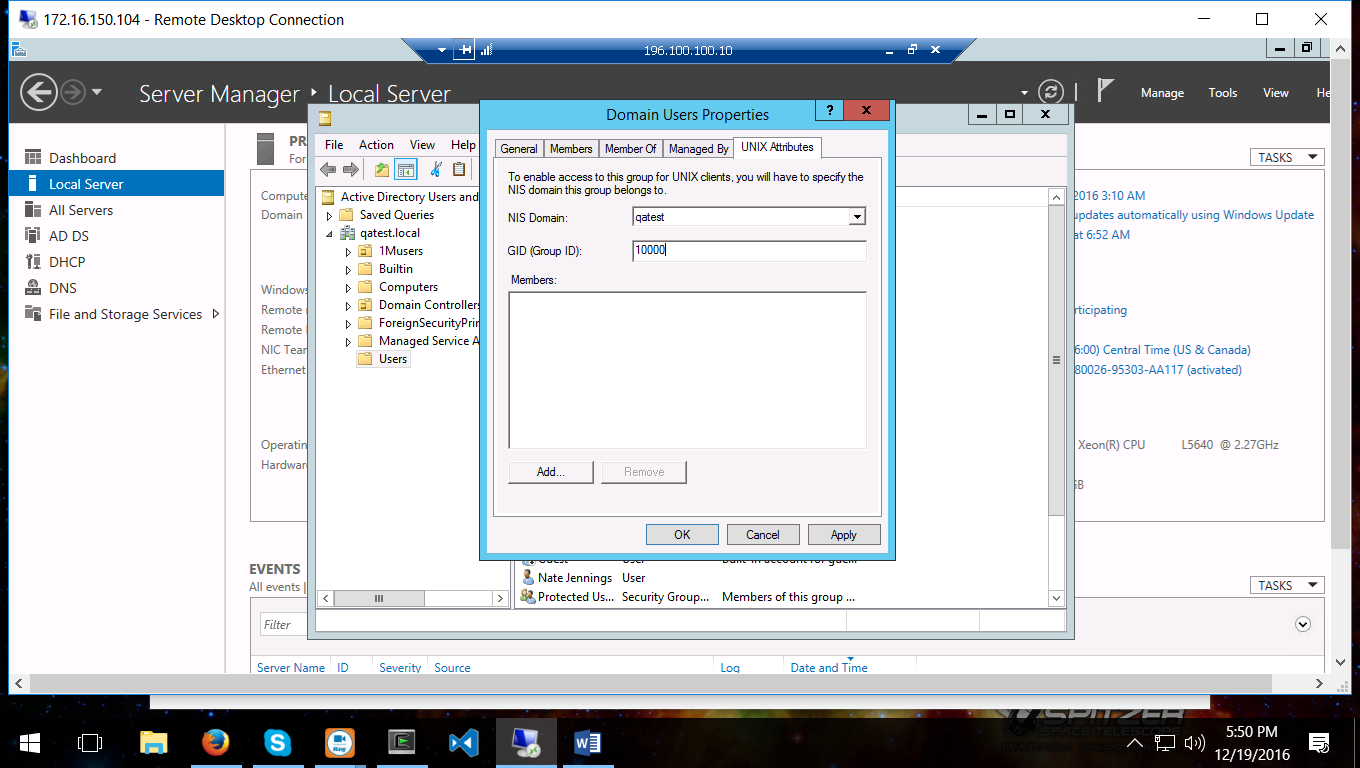
This screenshot shows the Adding of the Unix Attribute for the Domain Users:
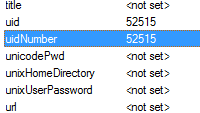
This Screenshot shows the UID and GID of another User:
- 7) SSH into the Primary SoftNAS as described here: https://www.softnas.com/helpdesk/index.php?/Knowledgebase/Article/View/1/0/softnas-kb-how-to-access-softnas-via-ssh
- 8) Run the following commands to view your NIS User information on the SoftNAS that was synced from the AD.
root@SoftNAS:~# getent passwd | grep SOFTNAS0
SOFTNAS0/kash:*:10005:10000:Kash Pande:/example/home/kash:/bin/ksh
And to see GID’s Mapped:
root@SoftNAS:~ # getent group | grep SOFTNAS0
SOFTNAS0/domain admins:x:10001:
SOFTNAS0/domain users:x:10000:
- 9) The above command shows that the users information is synced. And that we have the correct GID setting for the domain users. All users in that Group can now Sync to the SoftNAS Once the UID is set, as explained in Step 4.
- 10) We can now test by changing the ownership of the files:
root@SoftNAS:/tank/vol1# touch testfile
root@SoftNAS:/tank/vol1# ls -l
total 2
drwxrwxrwx 2 root root 3 Dec 19 11:39 .
drwxrwxrwx 3 root root 3 Dec 12 10:57 ..
-rw-r--r-- 1 root root 0 Dec 19 11:49 testfile
root@SoftNAS:/tank/vol1# chown "SOFTNAS0/kash:SOFTNAS0/domain users" testfile
root@SoftNAS:/tank/vol1# ls -l
total 2
drwxrwxrwx 2 root root 3 Dec 19 11:39 .
drwxrwxrwx 3 root root 3 Dec 12 10:57 ..
-rw-r--r-- 1 SOFTNAS0/kash SOFTNAS0/domain users 0 Dec 19 11:49 testfile
- 11) Now to review the Status on an NFSv4 that is NOT on the AD:
# mount -vt nfs -o vers=4 192.168.193.135:tank/vol1 /mnt
mount.nfs: timeout set for Mon Dec 19 11:04:21 2016
mount.nfs: trying text-based options 'vers=4,addr=192.168.193.135,clientaddr=192.168.193.221'
# cd /mnt
# ls -l
total 2
drwxrwxrwx 2 root root 3 Dec 19 11:39 .
drwxrwxrwx 3 root root 3 Dec 12 10:57 ..
-rw-r--r-- 1 10005 10000 0 Dec 19 11:49 testfile
- 12) We can see that the UID and the GID information is saved, and that the NFSv4 Server needs to be added to the Domain as per these instructions: https://access.redhat.com/documentation/en-US/Red_Hat_Enterprise_Linux/7/html/Windows_Integration_Guide/adding-linux-to-ad.html
- 13) Once Added you can see that the NFSv4 Client can now see the AD UID’s and GID’s:
root@NFSCLIENT:~# getent passwd | grep SOFTNAS0
SOFTNAS0/kash:*:10005:10000:Kash Pande:/example/home/kash:/bin/ksh
And to see GID’s Mapped:
root@NFSCLIENT:~ # getent group | grep SOFTNAS0
SOFTNAS0/domain admins:x:10001:
SOFTNAS0/domain users:x:10000:
And we can see the proper RFC2307 information:
# mount -vt nfs -o vers=4 192.168.193.135:tank/vol1 /mnt
mount.nfs: timeout set for Mon Dec 19 11:04:21 2016
mount.nfs: trying text-based options 'vers=4,addr=192.168.193.135,clientaddr=192.168.193.221'
# cd /mnt
# ls -l
total 2
drwxrwxrwx 2 root root 3 Dec 19 11:39 .
drwxrwxrwx 3 root root 3 Dec 12 10:57 ..
-rw-r--r-- 1 SOFTNAS0/kash SOFTNAS0/domain users 0 Dec 19 11:49 testfile
The NFSv4 Clients can use AD, or use RPCIDMAPd to sync NFSv4 files however, the /etc/passwd and /etc/group files must contain entries that resemble the ‘getent passwd/getent group” commands used to check UID’s and GID’s in previous steps.
You can now add Users and Groups to the CIFS Access and Control: https://www.softnas.com/docs/softnas/v3/html-reference-guide/configuring_cifs_shares.html